Microsoft 70-414 Practice Tests From People Who Created Microsoft 70-414 Exam(11-20)
QUESTION 11
Your network contains an Active Directory Rights Management Services (AD RMS) cluster named Cluster1. You plan to change Cluster1 to a new AD RMS cluster named Cluster2.
You need to ensure that all users retrieve the location of the AD RMS templates from Cluster2. What should you do?
A. Create an alias (CNAME) record named clusterl.contoso.com that points to Cluster2.
B. Modify the Service Connection Point (SCP).
C. Modify the templates file location of the rights policy templates.
D. Modify the exclusion policies.
Answer: B
QUESTION 12
Your network contains an Active Directory domain named contoso.com.
You deploy Active Directory Certificate Services (AD CS).
Your company, which is named Contoso, Ltd., has a partner company named Fabrikam, Inc. Fabrikam also deploys AD CS. Contoso and Fabrikam plan to exchange signed and encrypted email messages.
You need to ensure that the client computers in both Contoso and Fabrikam trust each other’s email certificates. The solution must prevent other certificates from being trusted.
What should you do?
More than one answer choice may achieve the goal. Select the BEST answer.
A. Implement an online responder in each company.
B. Exchange the root certification authority (CA) certificates of both companies, and then deploy the certificates to the Trusted Root Certification Authorities store by using Group Policy objects (GPOs).
C. Exchange the root certification authority (CA) certificates of both companies, and then deploy the certificates to the Enterprise Trust store by using Group Policy objects (GPOs).
D. Implement cross-certification in each company.
Answer: D
QUESTION 13
Your network contains an Active Directory domain named contoso.com. Your company has an enterprise root certification authority (CA) named CA1.
You plan to deploy Active Directory Federation Services (AD FS) to a server named Serverl. The company purchases a Microsoft Office 365 subscription.
You plan register the company’s SMTP domain for Office 365 and to configure single sign-on for all users.
You need to identify which certificate or certificates are required for the planned deployment. Which certificate or certificates should you identify? (Each correct answer presents a complete solution. Choose all that apply.)
A. a server authentication certificate that is issued by a trusted third-party root CA and that contains the subject name serverl.contoso.com
B. a server authentication certificate that is issued by CA1 and that contains the subject name Server1
C. a server authentication certificate that is issued by a trusted third-party root CA and that contains the subject name Server1
D. a server authentication certificate that is issued by CA1 and that contains the subject name serverl.contoso.com
E. self-signed server authentication certificates for serverl.contoso.com
Answer: A
Explanation:
Answer is just A (Server authentication certificate that is issued by a trusted third-party root CA and that contains the subject name serverl.contoso.com)
http://technet.microsoft.com/en-us/library/jj151794.aspx#bk_requirements
http://technet.microsoft.com/en-us/library/hh852419.aspx
QUESTION 14
Your network contains an Active Directory domain named contoso.com. The network contains two servers named Server1 and Server2.
You deploy Active Directory Certificate Services (AD CS). The certification authority (CA) is configured as shown in the exhibit. (Click the Exhibit button.)
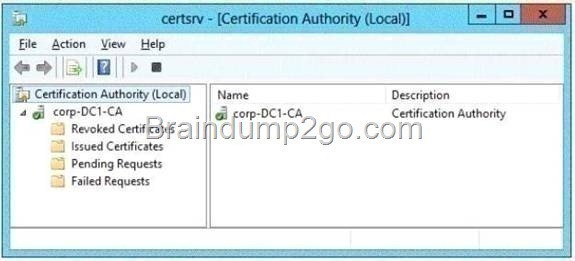
You need to ensure that you can issue certificates based on certificate templates.
What should you do?
A. On Server1, install the Network Device Enrollment Service role service.
B. Configure Server2 as a standalone subordinate CA.
C. On Server1, uninstall, and then reinstall AD CS.
D. On Server1, run the Add-CertificateEnrollmentPolicyServer cmdlet.
Answer: C
QUESTION 15
Your network contains an Active Directory domain named contoso.com.
You plan to deploy an Active Directory Federation Services (AD FS) farm that will contain eight federation servers.
You need to identify which technology or technologies must be deployed on the network before you install the federation servers. Which technology or technologies should you identify? (Each correct answer presents part of the solution. Choose all that apply.)
A. Network Load Balancing (NLB)
B. Microsoft Forefront Identity Manager (FIM) 2010
C. The Windows Internal Database feature
D. Microsoft SQL Server 2012
E. The Windows Identity Foundation 3.5 feature
Answer: AD
Explanation:
Best practices for deploying a federation server farm We recommend the following best practices for deploying a federation server in a production environment:
* (A) Use NLB or some other form of clustering to allocate a single IP address for many federation server computers.
* (D) If the AD FS configuration database will be stored in a SQL database, avoid editing the SQL database from multiple federation servers at the same time.
* If you will be deploying multiple federation servers at the same time or you know that you will be adding more servers to the farm over time, consider creating a server image of an existing federation server in the farm and then installing from that image when you need to create additional federation servers quickly.
* Reserve a static IP address for each federation server in the farm and, depending on your Domain Name System (DNS) configuration, insert an exclusion for each IP address in Dynamic Host Configuration Protocol (DHCP). Microsoft NLB technology requires that each server that participates in the NLB cluster be assigned a static IP address.
Reference: When to Create a Federation Server Farm
QUESTION 16
Your network contains an Active Directory domain named contoso.com. The network contains a server named Server1 that runs Windows Server 2012. Server1 has the Active Directory Certificate Services server role installed. Serve1l is configured as an offline standalone root certification authority (CA).
You install the Active Directory Certificate Services server role on Server2 and configure the server as an enterprise subordinate CA.
You need to ensure that the certificate issued to Server2 is valid for 10 years.
What should you do first?
A. Modify the registry on Server1.
B. Modify the registry on Server2.
C. Modify the CAPolicy.inf file on Server2.
D. Modify the subordinate CA certificate template.
E. Modify the CAPolicy.inf file on Server1.
Answer: A
Explanation:
http://technet.microsoft.com/en-us/library/hh831348.aspx
http://marckean.wordpress.com/2010/07/28/build-an-offline-root-ca-with-a-subordinate-ca/
Point 4. Setup the root CA to issue certificates with an expiry date of 10 years (will issue to the Sub CA for 10 years)
Change the following registry path on the Root CA -HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\CertSvc\Configuration\Root-CA\ValidityPeriodUnits
Change the REG_DWORD decimal value to 10.
This changes it to 10 years, so when the Sub CA gets a certificate, it won’t expire for another 10 years.
QUESTION 17
Your company has an office in New York. Many users connect to the office from home by using the Internet.
You deploy an Active Directory Certificate Services (AD CS) infrastructure that contains an enterprise certification authority (CA) named CA1. CA1 is only available from hosts on the internal network.
You need to ensure that the certificate revocation list (CRL) is available to all of the users.
What should you do? (Each correct answer presents part of the solution. Choose all that apply.)
A. Create a scheduled task that copies the CRL files to a Web server.
B. Run the Install-ADCSWebEnrollment cmdlet.
C. Run the Install-EnrollmentPolicyWebService cmdlet.
D. Deploy a Web server that is accessible from the Internet and the internal network.
E. Modify the location of the Authority Information Access (AIA).
F. Modify the location of the CRL distribution point (CDP).
Answer: ADF
Explanation:
D: access to CRLs for the ‘Internet scenario’ is fully supported and includes the following features:
CRLs will be located on Web servers which are Internet facing. CRLs will be accessed using the HTTP retrieval protocol. CRLs will be accessed using an external URL of http://dp1.pki.contoso.com/pki
F: To successfully authenticate an Internet Protocol over Secure Hypertext Transfer Protocol (IP- HTTPS)-based connection, DirectAccess clients must be able to check for certificate revocation of the secure sockets layer (SSL) certificate submitted by the DirectAccess server. To successfully perform intranet detection, DirectAccess clients must be able to check for certificate revocation of the SSL certificate submitted by the network location server. This procedure describes how to do the following:
Create a Web-based certificate revocation list (CRL) distribution point using Internet Information Services (IIS)
Configure permissions on the CRL distribution shared folder Publish the CRL in the CRL distribution shared folder Reference: Configure a CRL Distribution Point for Certificates
QUESTION 18
Your network contains five Active Directory forests.
You plan to protect the resources in one of the forests by using Active Directory Rights Management Services (AD RMS) Users in all of the forests will access the protected resources. You need to identify the minimum number of AD RMS clusters required for the planned deployment. What should you identify?
A. One root cluster and five licensing clusters
B. One licensing cluster and five root clusters
C. Five root clusters
D. Five licensing clusters
Answer: C
QUESTION 19
Your network contains a Hyper-V host named Host1. Host1 hosts 25 virtual machines. All of the virtual machines are configured to start automatically when Host1 restarts.
You discover that some of the virtual machines fail to start automatically when Host1 restarts and require an administrator to start them manually.
You need to modify the settings of the virtual machines to ensure that they automatically restart when Host1 restarts.
Which settings should you modify?
A. Memory weight
B. Maximum RAM
C. Startup RAM
D. Minimum RAM
Answer: C
QUESTION 20
Your network contains multiple servers that run Windows Server 2012. The network contains a Storage Area Network (SAN) that only supports Fibre Channel connections. You have two failover clusters. The failover clusters are configured as shown in the following table.

You plan to implement 15 highly available virtual machines on Cluster2. All of the virtual machines will be stored in a single shared folder. You need to ensure that the VHD files of the virtual machines can be stored on the SAN. What should you do? (Each correct answer presents a complete solution.Choose all that apply.)
A. From a node in Cluster2, create a Virtual Fibre Channel SAN.
B. From a node in Cluster1, create a Virtual Fibre Channel SAN.
C. From Cluster1, add the iSCSI Target Server cluster role.
D. From Cluster1, configure the clustered File Server role of the File Server for scale-out application
data type.
Answer: CD
Explanation:
* After the virtual machines are connected to the storage system using the virtual Fibre Channel components shared storage can be used by each VM, which enables Hyper-V guest clustering. Before the virtual Fibre Channel features were available, Hyper-V guest machines were limited to iSCSI connections to enable shared storage for guest clustering.
* A new feature in Windows Server 2012 Hyper-V is the ability to create a virtual Fibre Channel SAN. Each guest VM created on Windows Server 2012 includes a new option Add hardware Fibre Channel cards, which can be attributed to World Wide node names(WWNN) and select the virtual combine Virtual SAN Fibre Channel adapters.
Download Braindump2go’s Latest Microsoft 70-414 Dump Full Version For Free: http://www.braindump2go.com/70-414.html